Researchers identified super hacker after series of attacks on government websites that started in 2013
The real identity if Brazilian individual from the city of Uberlândia got exposed by researchers from Check Point, who reported on VandaTheGod’s activity for years. The hacker left a digital trail that led to this discovery. The person was responsible for defacing over 4800 government sites and was reported for law enforcement. This report includes all the social media accounts like facebook and Twitter and more linked with VandaTheGod and activities throughout these platforms. This hacker targeted government websites in numerous countries, including: Brazil, the Dominican Republic, Trinidad and Tobago, Argentina, Thailand, Vietnam, and New Zealand.
It was obvious that VandaTheGod enjoyed social media and the attention that the hacktivism brought because Twitter accounts praised all the website hackings. The individual is known for targeting entities and people in the United States, Australia, Netherlands, Italy, South Africa, Canada, the UK, Germany, as far as researchers know.
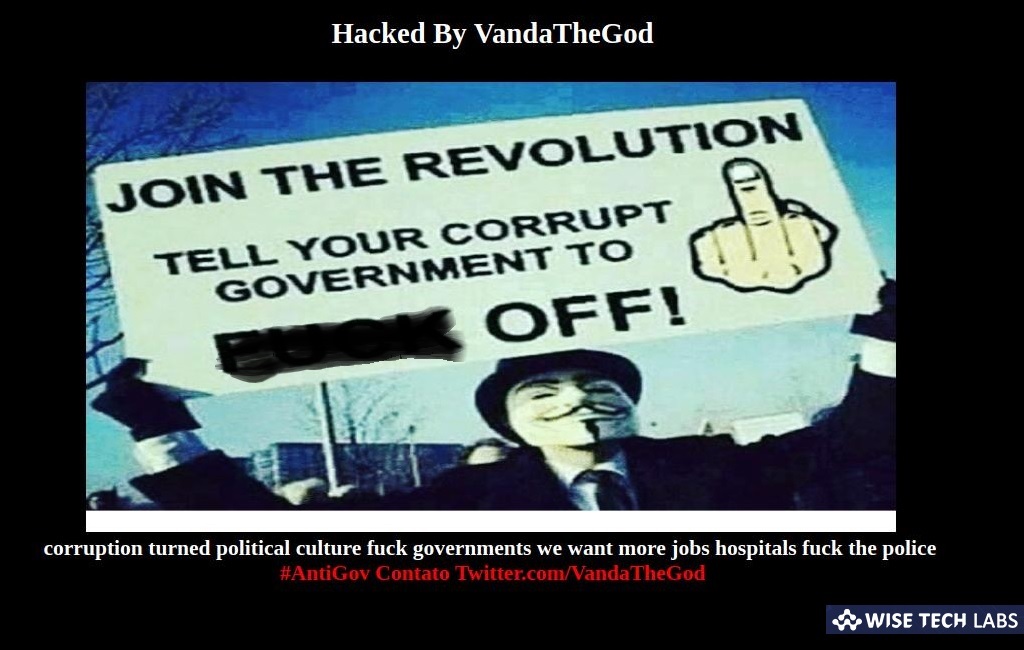
The investigation exposed messages left on defaced websites and this information implied that attacks were motivated by the anti-government sentiment. Different types of messages, though, exposed the identity of the hacker because social media activities left the trail that routed to the doorsteps of, know an identified member of the Brazilian Cyber Army M.R.
Social media digital trail led to the personal account of this hacker
The person behind this VandaTheGod persona had multiple aliases in the past, and those social media profiles were all indicated and linked to together. VandaTheGod enjoyed the attention and was especially active on Twitter, and links to the account sometimes got added to the message on compromised websites. This was a great confirmation that the attacker was the one who managed the Twitter account.
Language used was another fact that revealed a lot. Many posts on the account were written in Portuguese. Also, the hacker himself claimed to be a part of BCA by even displaying the logo in screenshots of hacked sites and accounts. The email that was used to register websites for the Brazilian Cyber Army and VandaTheGod domains gave away the real identity when researchers found the Facebook profile belonging to Vanda De Assis and further cross-posts analysis tied the identified individual M.R to VandaTheGod hacktivism.
Anti-government activities and regular hacking for profit
Hacktivist was written all over the VandaTheGod activities because defaced Brazilian government sites with hashtags #PrayforAmazonia were a direct response to burning of the Amazon rain forests. This attacker was focused on campaigns that had anti-government factor and were carried out against social injustices and corruption.
VandaTheGod stated that all the campaigns will stop once the number of hacked government sites reaches 5,000. However, there were different instances in these campaigns. For example, researchers note that a few times the attacker revealed stolen credit card details and shared screenshots and photos with stolen number details.
It was the personal goal of the attacker even though VandaTheGod held attacks against governments with political motivation. However, attacks on public figures, universities, and hospitals were not only for hacking. When records of 1 million patients from New Zealand got stolen, the hackers offered information for sale for $200.
Hacktivism often comes on the thin line between criminal activities and digital vandalism, as researchers state:
VandaTheGod has proven with numerous successful attacks against reputable websites, that hacktivism often crosses a line into further criminal activity, such as credentials and payment-card theft, and indeed share their exploits and techniques with the wider cyber-crime community – making them a very real danger to online security.
“VandaTheGod has proven with numerous successful attacks against reputable websites, that hacktivism often crosses a line into further criminal activity, such as credentials and payment-card theft,” said Check Point.







What other's say